Zoom Single Sign-On
How to configure Zoom multi-factor authentication (MFA) with Gluu+WWPass Identity Provider
The Zoom MFA implementation consists of two parts: first you deploy Gluu server with WWPass authentication and, second, you configure the Gluu server and Zoom to work together.
Part 1. Implement Gluu+WWPass server
You can find the software modules and instructions for Gluu+WWPass server implementaion in our GitHub project.
When done, proceed with the second part:
Part 2. Configure multi-factor authentication to Zoom with Gluu+WWPass IdP
Before you begin
While configuring SAML login, keep the Zoom admin account always open in two browsers. In case you made a configuration error and switch to non-functional SAML login, this second browser may help you to rollback.
Prerequisites
We assume you have administrative rights in your Zoom business account as well as in your company Gluu server. Throughout this manual we use
https://mygluu.comas a URL of Gluu serverhttps://mycorp.zoom.usas your Zoom Vanity URL
Substitute your own real addresses.
Zoom admin page
Login to your Zoom business account at https://mycorp.zoom.us
In the left column, select Advanced -> Single Sign On, click Enable button
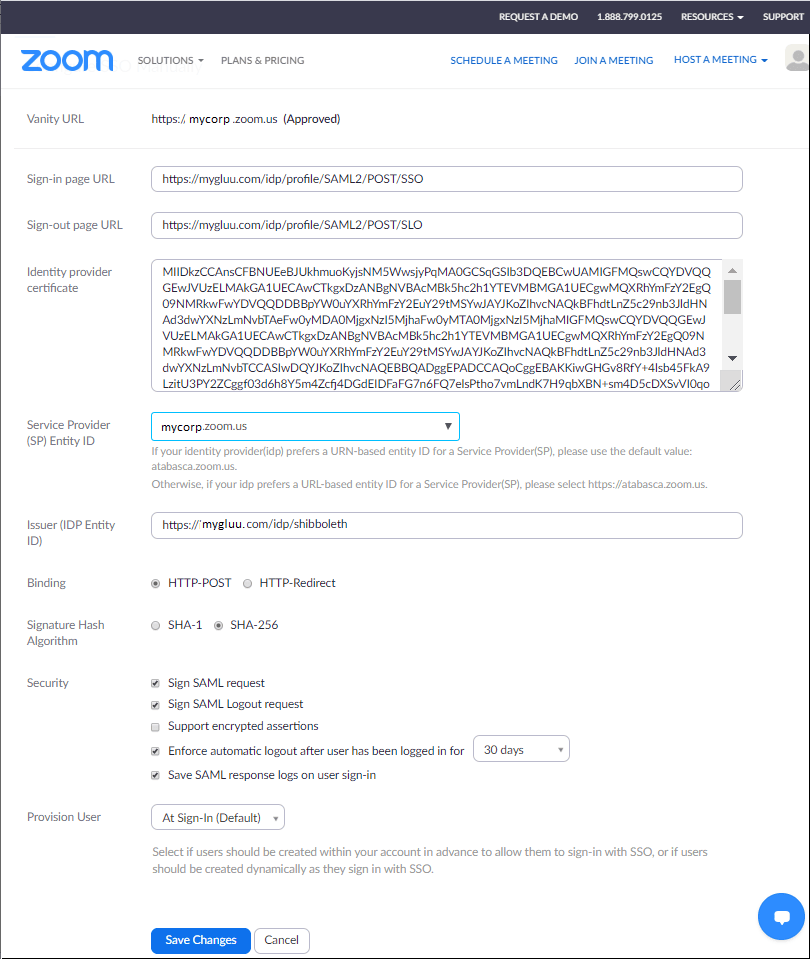
Fill in the following parameters:
- Sign-in page URL:
https://mygluu.com/idp/profile/SAML2/POST/SSO - Sign-out page URL:
https://mygluu.com/idp/profile/SAML2/POST/SLO - Service Provider Entity ID: mycorp.zoom.us
- Issuer (IdP Entity ID):
https://mygluu.com/idp/shibboleth - Binding: HTTP Post
- Signature hash algorithm: SHA-256
- Also check:
- YES - Sign SAML request
- YES - Sign SAML Logout request
- NO - Support encrypted assertions
- 30 days - Enforce automatic logout after user has been logged in for 30 days
- YES - Save SAML response logs on user sign-in
To fill the Identity provider certificate, go to https://mygluu.com/idp/shibboleth URL of your Gluu server. Select and copy the internals of signing certificate
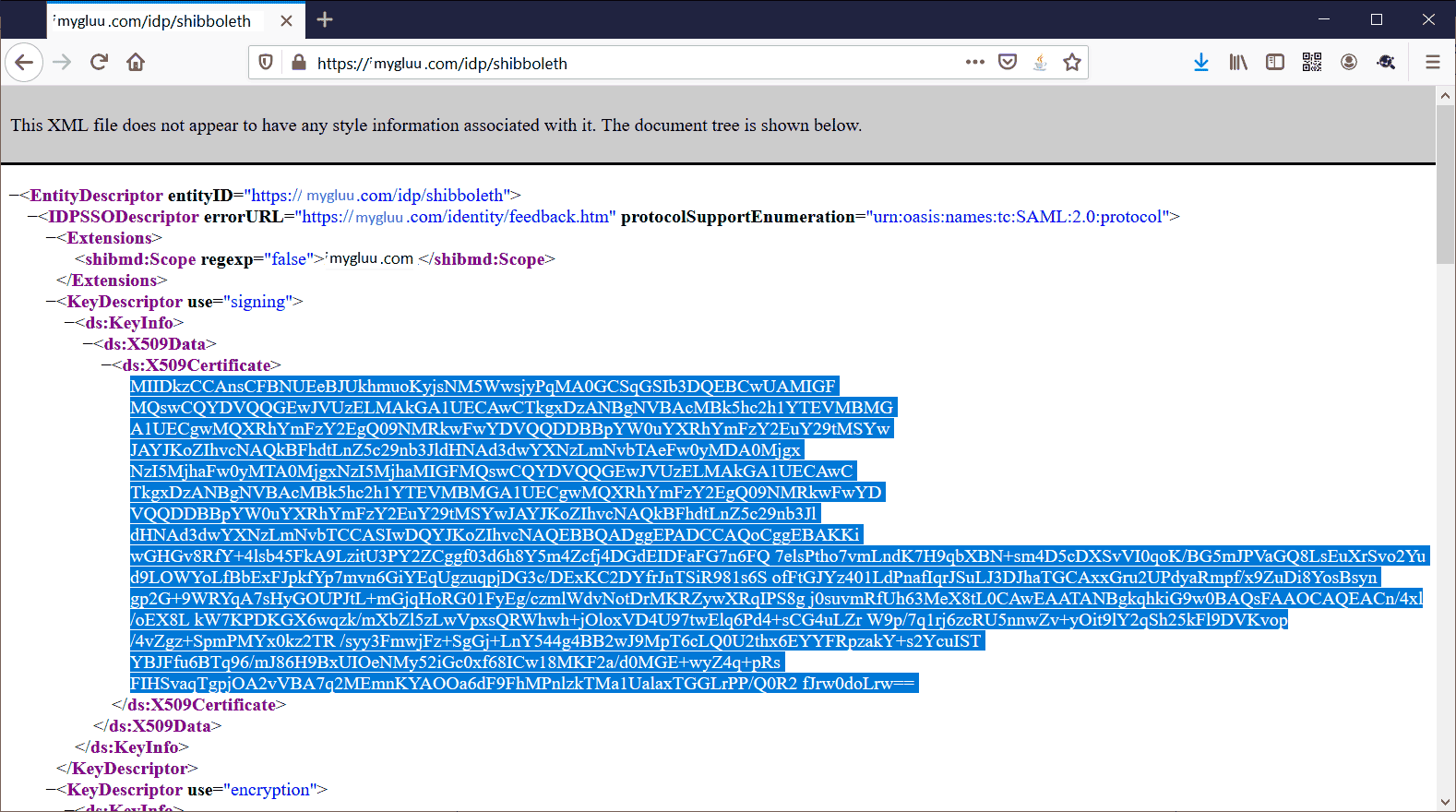
Paste the text to the Identity Provider Certificate field of the Zoom SAML admin page.
Later on, when you are comfortable with SAML authentication to Zoom, you can set "Support Ecnrypted Assertions" to "YES" and reduce "Enforce automatic logout after user has been logged in for" to 30 minutes.
Next, select SAML Response Mapping tab and fill it as follows:
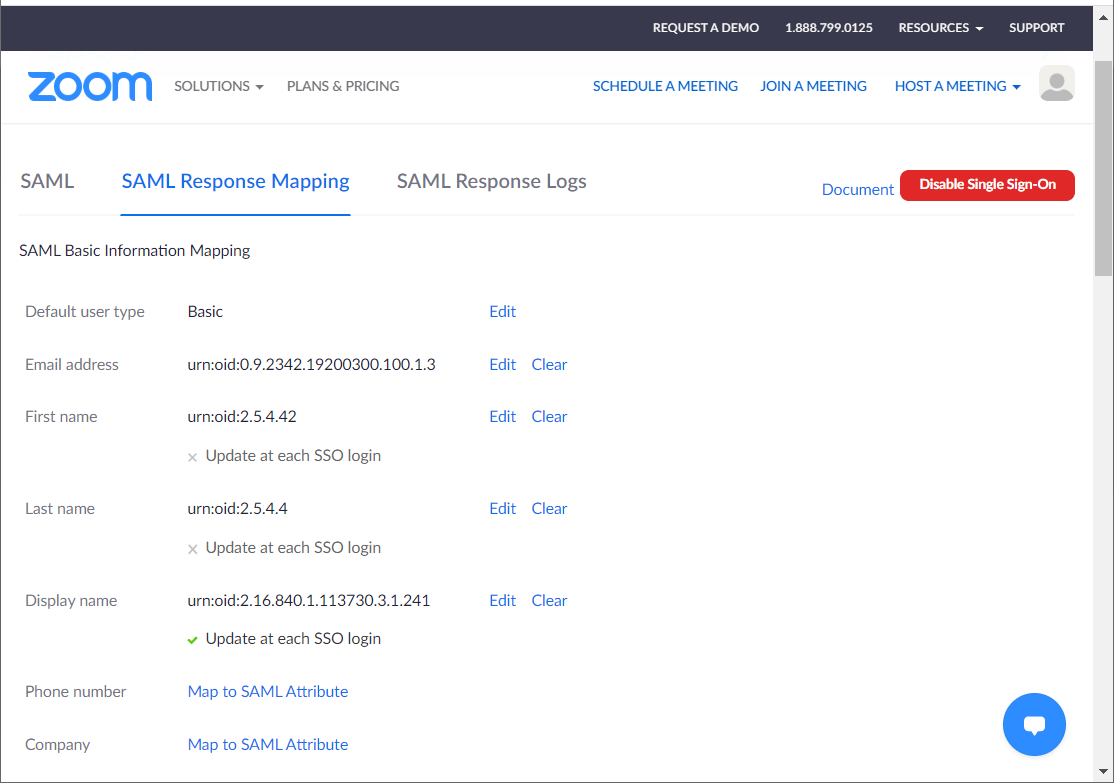
For reference, here are the oid values (Zoom sets these oids automatically):
- Email address
urn:oid:0.9.2342.19200300.100.1.3 - First name
urn:oid:2.5.4.42 - Last name
urn:oid:2.5.4.4 - Display name
urn:oid:2.16.840.1.113730.3.1.241
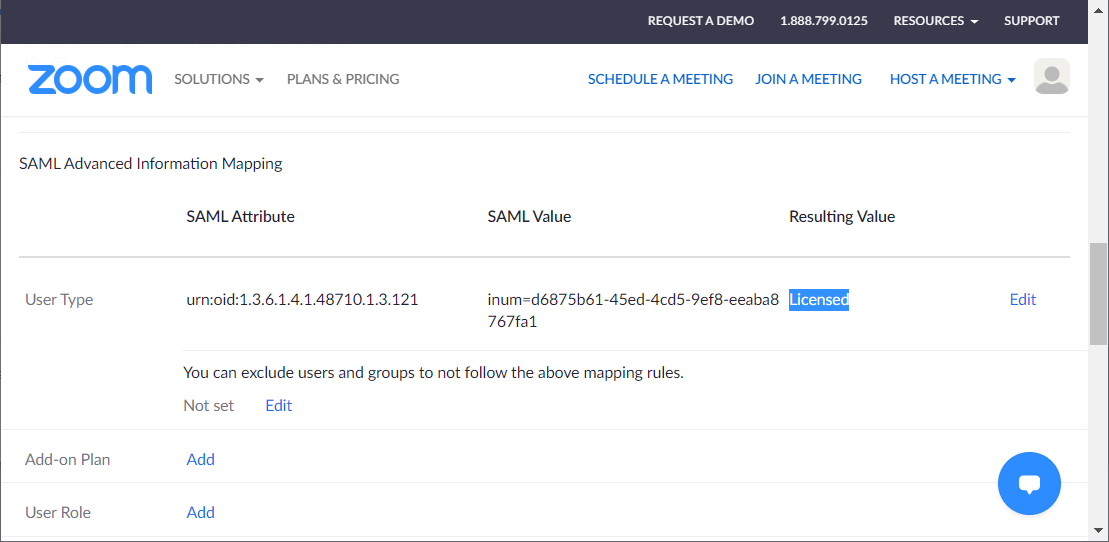
You can control Zoom user type (Basic, Licensed) directly from Gluu/AD by adding the user to the particular group. Scroll the page down to "SAML Advanced Information Mapping" and cofigure the "User type" entry:
- SAML Attribute
urn:oid:1.3.6.1.4.1.48710.1.3.121 - SAML value
inum=d6875b61-45ed-4cd5-9ef8-eeaba8767fa1 - Resulting Value
Licensed
Gluu SAML
Open admin page of your Gluu server, select SAML -> Add Trust Relationships in the left pane.
Fill the page as shown below. Select additional attributes Display Name, Email, First Name, Last Name, and Username from the right pane:
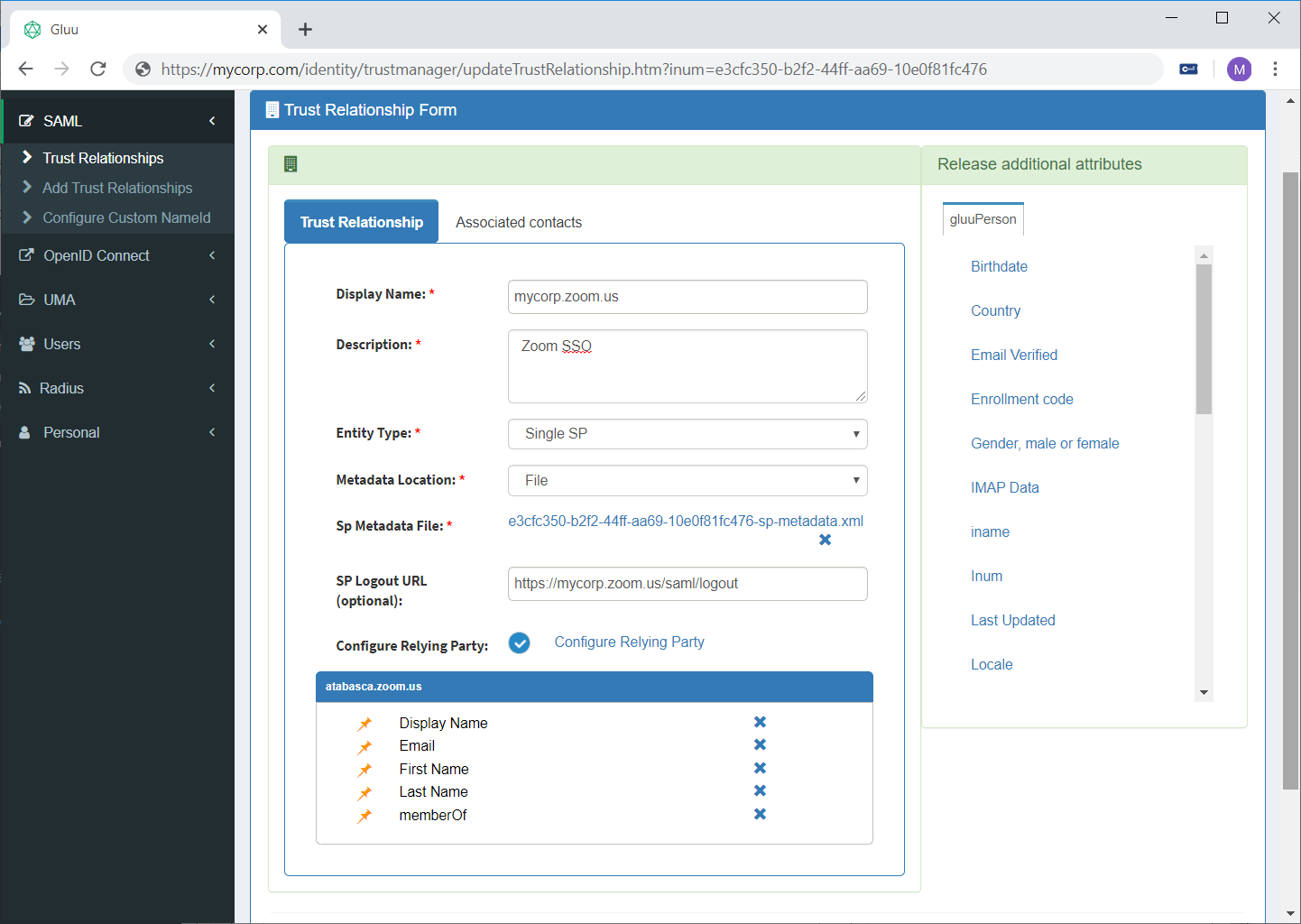
If you add “member Of” attribute, all user groups will be sent to Zoom (urn:mace:dir:attribute-def:memberOf, urn:oid:1.3.6.1.4.1.48710.1.3.121)
Download Zoom metadata file using URL https://mycorp.zoom.us/saml/metadata/sp. In the Gluu SAML configuration page, select Metadata Location: File, click Choose file button and point to the downloaded metadata file.
Finally, click Activate button at the bottom of the “Trust Relationships" form.
Now the Gluu server is configured.
How to debug
Zoom logs all the SAML assertions. Switch to SAML Response Logs tab on the Zoom Advanced -> Single Sign On page to see transaction details.
SAML logs can be found on the Gluu server, see directory /opt/gluu-server/opt/shibboleth-idp/logs
To see SAML messages in the Firefox browser, install SAML-tracer extension.